SOC as a Service
Continuous protection of the entire company as a subscription
There are many moving elements when it comes to keeping a business secure. H-X puts all of the parts together so you don’t have to. Buying an external service of the Security Operations Center (SOC) is an effective and efficient alternative to investments in the implementation and support of your own SOC.
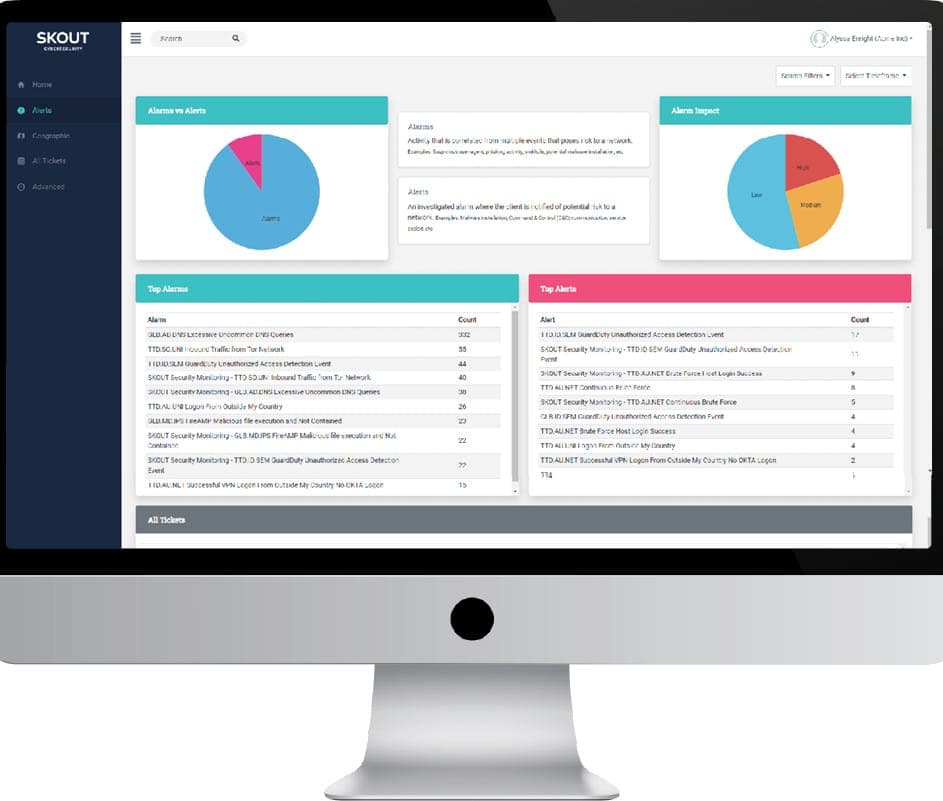
We use Splunk and FortiSIEM platforms for our Security Operations Center as a Service (SOCaaS). It is a managed solution that collects, aggregates, and normalizes log data from hundreds of sources for AI-enabled analysis using an analytics platform, threat intelligence, SIEM, and 24/7/365 Security Operations Center. The solution identifies threats such as incorrect logins, coordinated attacks, multi-factor bypass, and rogue agents.
“Three pillars” of our SOC
- Technology: log management, security event and incident management, event sources, security orchestration automation & response, user behavior analytics and machine learning, threat hunting, etc.
- Processes: technological, business, analytical, operational, communications, etc.
- People: IT and security engineers, security analytics, incident response team, etc.

Technology capabilities
- Log management platforms
- User behavior & Entity analysis
- Machine learning
- Orchestration & Response
- Digital Forensics
- Distributed cloud platform with high availability architecture, etc.
Our capabilities include monitoring the most popular server platforms, network technologies, applications, databases, virtualization platforms, storage, backups, cloud platforms, etc.
SOC levels
- Tier 1 (Level 1) – Alert Analysts continuously monitor the alert queues; triage security alerts; monitor the health of security sensors and endpoints; collect data and context necessary to initiate Tier 2 work.
- Tier 2 (Level 2) – Incident Responders perform deep-dive incident analysis by correlating data from various sources; determine if a critical system or data set has been impacted; advise on remediation; provide support for new analytic methods for detecting threats.
- Tier 3 (Level 3) – Subject Matter Experts and Threat Hunters possess in-depth knowledge of network, endpoint, threat intelligence, forensics, and malware reverse engineering, as well as the functioning of specific applications or underlying IT infrastructure; act as incident “hunters”, not waiting for incidents to occur; closely involved in developing, tuning and implementing threat detection analytics.
We will design the most suitable defense machine to fit your specific risk profile.
How to choose a SOC-as-a-service provider?
When choosing your SOCaaS supplier, check if they provide:
- Compliance with the standards and regulatory requirements your organization has to meet (PCI DSS, etc.).
- Raw log storage during the period you need.
- Flexibility in SIEM and SOC staff location according to your preferences and restrictions.
- Security hardening services.
- SIEM platform of your preference.
- Multi-tenant management consoles.
- Cyber risk insurance.
Pay attention to the SLA, for example:
- Tier 1 – incident detection and initial notification should be within 1 hour. Possibility to receive initial Tier 1 notifications.
- Tier 2 – incident verification and notification within 2 hours. In case of a no-authority SOC (monitoring only), the maximum percentage of false positives. In case of a full-authority SOC, full recovery within 72 hours.
- Tier 3 – the number of shared compromise indicators, the number of open sources, proprietary threat analytics sources, and Deep Web and Dark Web sources.
Basic SOC service
- Monitoring, detection, and analysis of potential intrusions in real-time and through historical trending on security-relevant data sources.
- Response to confirmed incidents, by notifying about security incidents (escalations) with information about the attacks, threats, vulnerabilities, affected systems, and recommendations on how to mitigate the incidents and vulnerabilities.
- Participation in resource coordination, and taking of timely and appropriate countermeasures for incident response.
- Tier 1 (alert analysts), Tier 2 (incident responders), and Tier 3 (subject matter experts and threat hunters).
- Technologies: Splunk, FortiSIEM, Kubernetes, Graylog, Elasticsearch, Logstash, Kibana, syslog-ng, Ansible, etc.
Service summary
| ⏳ Duration of delivery | Continuous. You can subscribe to managed compliance on a monthly basis and stop the subscription any day. |
| 🎁 Can it be free or have a testing period? | Free consultation and initial analysis of business requirements. |
| 💼 What type of business needs it? | Any business that has a significant online presence or relies on technology for its operations, or is subject to regulatory compliance requirements. |
| 💡 When is this service needed? | When you want to proactively monitor cyber threats, but do not have the resources to establish an effective in-house security operations center (SOC). |
| 📈 Your profit | Reducing cyber security risk and expenses for in-house security personnel and technology infrastructure. |
| ⚙️ Our methods and tools | SIEM, IDPS, log management, threat intelligence feeds, vulnerability scanners, security analytics platforms, AI, incident response playbooks, etc. |
| 📑 Deliverables | Reports on security events, incident response plans, security recommendations, remediation guidance, monitoring, KPIs, threat intelligence feeds, etc. |
Learn more about our additional services and business cases. Send the form below to order SOC as a service. Get a free consultation.
REQUEST A QUOTE